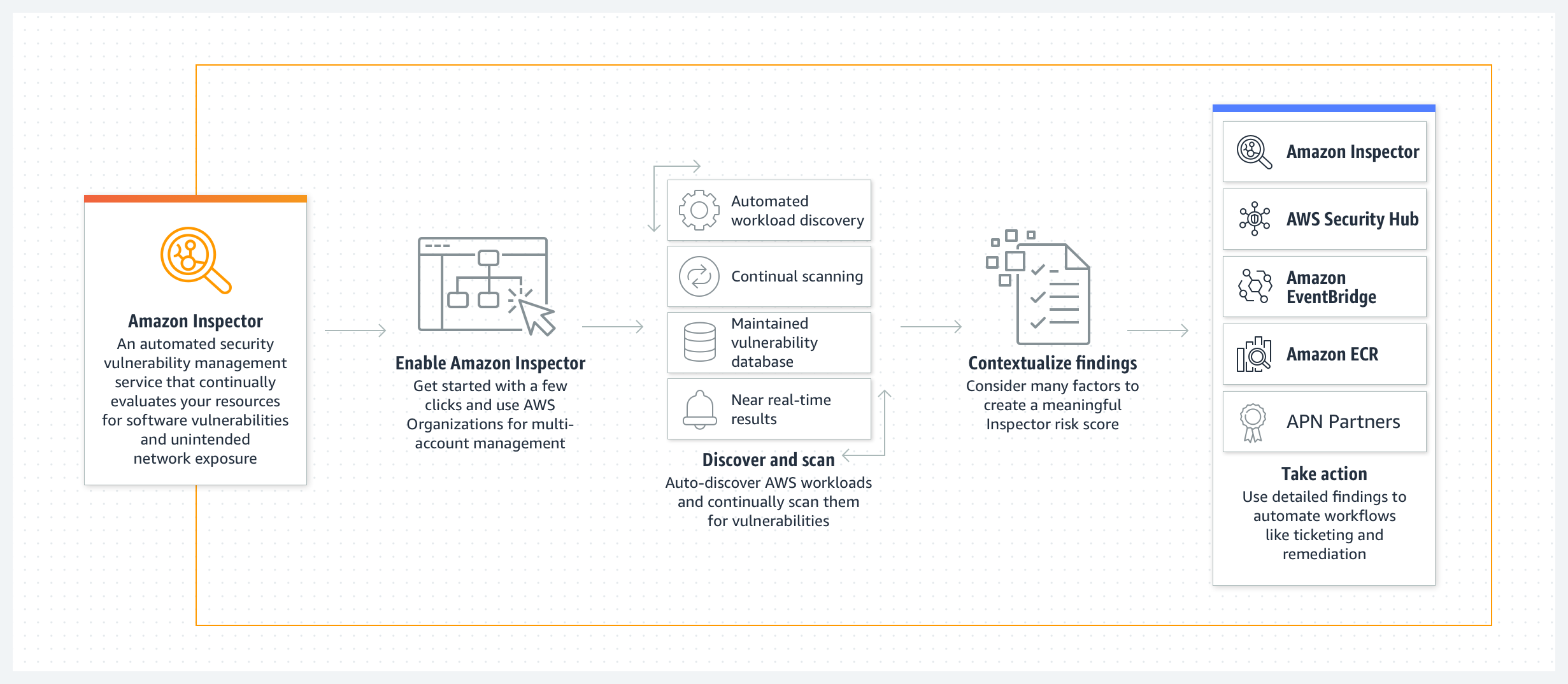
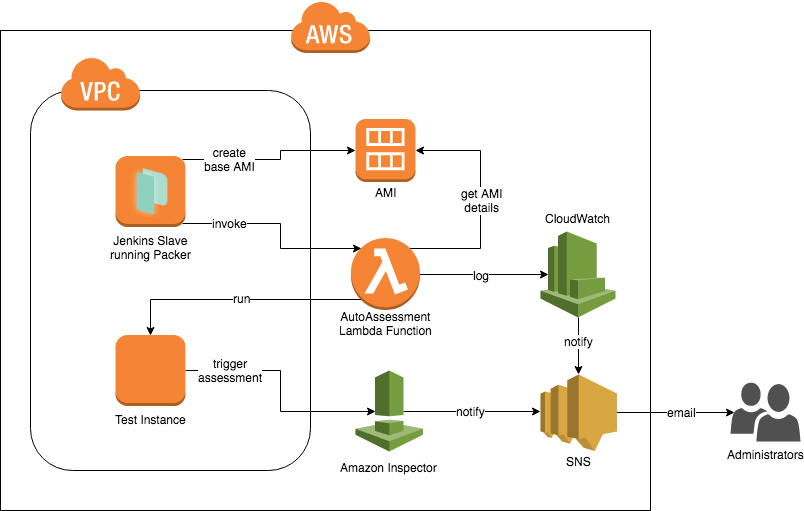
How to Set Up Continuous Golden AMI Vulnerability Assessments with Amazon Inspector | AWS Security Blog
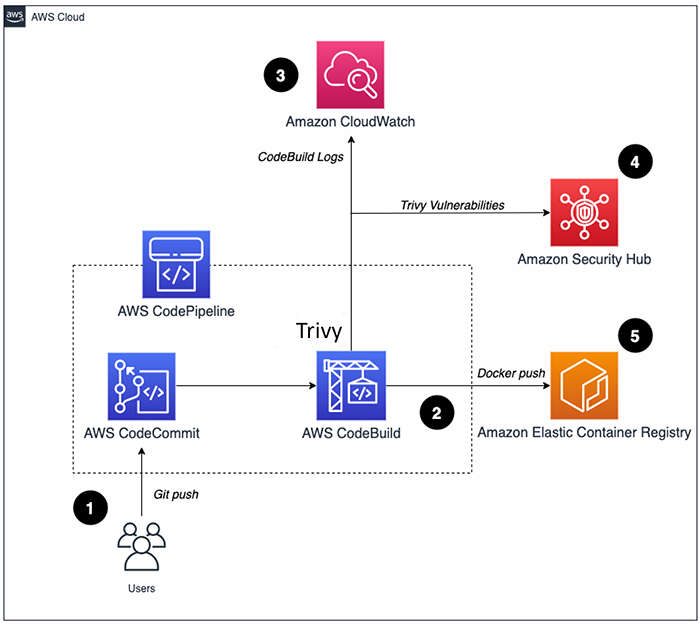
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog
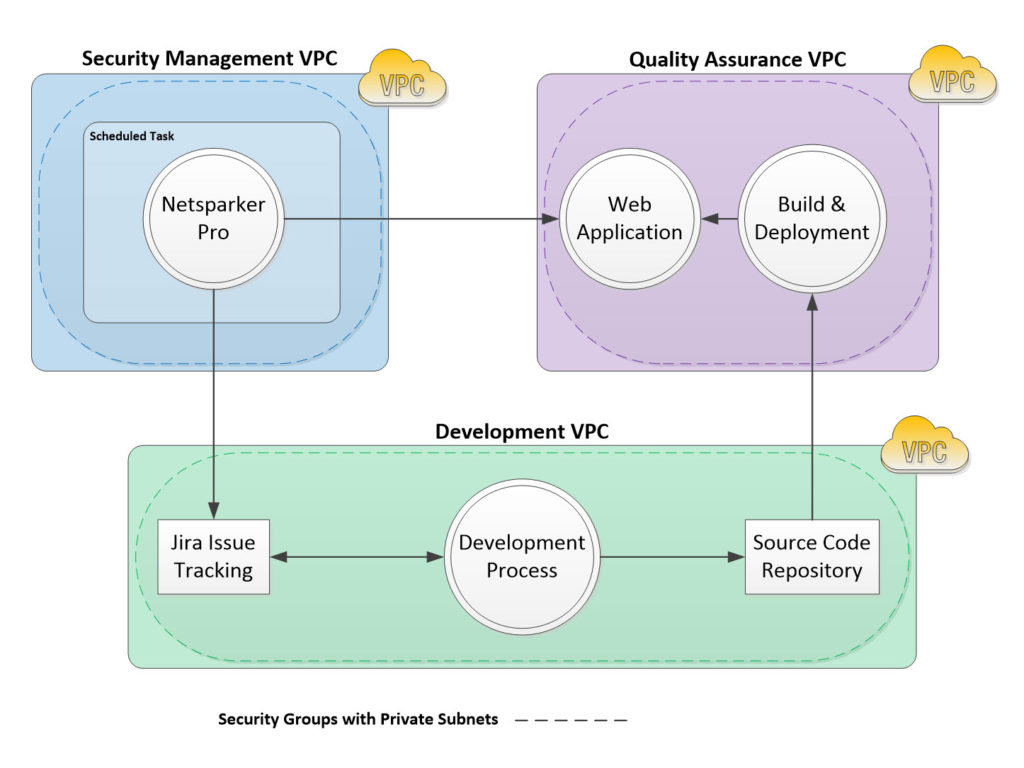
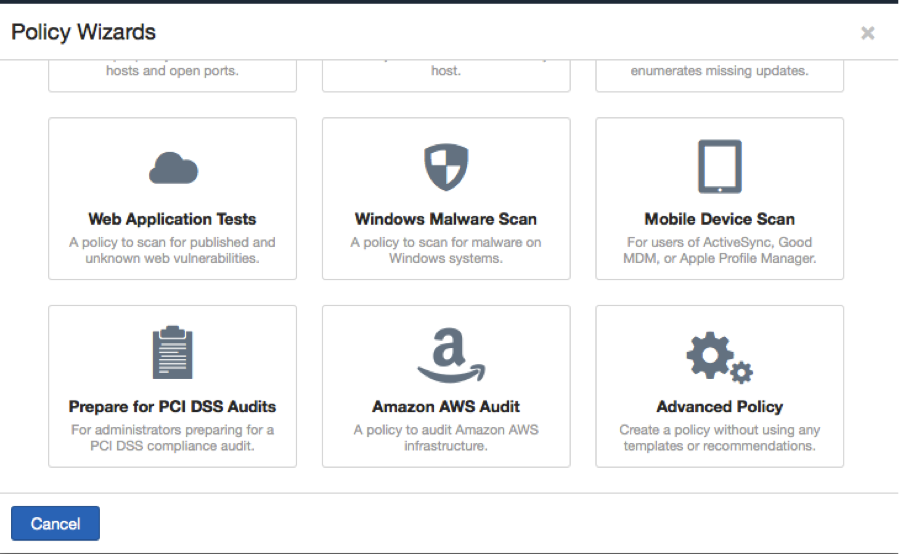
Automating Web Application Vulnerability Scanning in Amazon Web Services with Netsparker - Strong Crypto